etsadmin
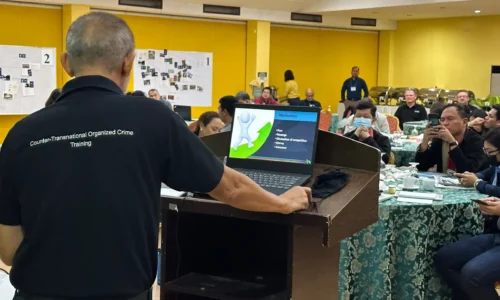
CTOC Module 08a: Open Source Intelligence (OSINT) Techniques (Theoretical)
Open Source Intelligence (OSINT) Techniques(Theoretical) outlines the various types of online resources that can be used to obtain information on suspects who are under investigation.
CTOC Module 07: Digital Forensics and Communications Exploitation
Digital Forensics and Communications Exploitation explains the various types of electronic equipment from which information can be extracted and analyzed.
CTOC Module 06: Acquisition and Handling of Evidence
Acquisition and Handling of Evidence provides in-depth examination of the types of evidence that can be collected, including the procedures and requirements for correct collection, handling, sealing...
CTOC Module 05: Specialized Investigative Techniques – Controlled Deliveries
Specialized Investigative Techniques illustrates Controlled Deliveries (CDs) as a specialized investigative technique that can be used in transnational organized crime investigations.
CTOC Module 04: Document Exploitation
Document Exploitation (DOMEX) illustrates the identification and collection of documents required for successfully investigating TOC cases.
CTOC Module 03b: Source Management
Source Management illustrates the methods for managing informants and sources of information.
CTOC Module 03a: Development of Informants
Development of Informants illustrates the methods for developing informants as sources of information.
CTOC Module 02: Introduction to Transnational Organized Crime
Introduction to Transnational Organized Crime is about understanding the supply chains utilized by the criminal group being investigated.